Key points
- Enterprises face increasing threats, with 75% reporting sensitive cloud data in 2023 and 39% experiencing breaches in the same year.
- Comprehensive data protection is vital for preventing intellectual property theft and financial losses and ensuring legal compliance.
- Being proactive in protecting sensitive data by limiting access, encrypting data, employing firewalls, and performing regular audits, along with other measures, is essential.
- Cloud providers, like Liquid Web, offer managed hosting, high availability infrastructure, regulatory compliance, and security add-ons for robust data security.
For enterprises that handle sensitive, confidential, and classified data, data security should be a top priority.
In 2023, three-quarters of businesses said at least 40% of their data stored in the cloud is classified as sensitive. In 2021, only 49% of businesses carried that much important data in the cloud. The same study showed 39% of businesses reported experiencing a cloud data breach in the last year.
A data breach can be financially and reputationally devastating. So, what steps should enterprises take to protect their data? This guide to enterprise data security will include all that and more:
What is enterprise security?

Enterprise data security encompasses all of the strategies and practices that organizations implement to protect sensitive information, such as a business’s supply chain, manufacturing processes, inventory, customers, employees, intellectual property (IP), and trade secrets.
Other types of sensitive data include Personally Identifiable Information (PII), like names, addresses, and Social Security numbers; financial records; health records; voice, video, and chat logs; security logs and passwords; and legal correspondence.
Chances are, your business handles some, if not most, of this data. And the effects of it getting into the wrong hands could be catastrophic for your business and those whose information is leaked.
It’s impossible to lock this data down entirely, so a crucial part of enterprise data protection is designing security systems to let authorized users still access it — while avoiding any slipups that could let unwanted eyes in.
The importance of enterprise data security

Beyond the immediate concern of safeguarding sensitive information, the benefits of implementing comprehensive data protection strategies are extensive.
Safeguarding intellectual property
Enterprises often act as custodians of valuable IP, ranging from proprietary software and unique business processes to invaluable research data that provides a competitive edge.
According to the Commission on the Theft of American Intellectual Property, the U.S. economy loses hundreds of billions of dollars every year due to IP theft.
Preventing financial loss
The repercussions of a data breach extend well beyond compromised information.
Companies face significant financial implications in the aftermath of an extensive data breach.
Here are a few of the potential costs:
- Investigating and remediating the incident.
- Downtime and lost productivity.
- Legal actions, including suing offenders, sending out Cease and Desist letters, and dealing with lawsuits.
- Regulatory fines.
- Investing in heightened security measures.
- Customer compensation associated with stolen PII.
- Increased cybersecurity insurance premiums.
- Loss of customers due to reputational damage.
Legal and regulatory compliance
Many industries are governed by strict regulations that mandate the protection of sensitive information. These are a few policies you may need to comply with:
- HIPAA (Health Insurance Portability and Accountability Act of 1996): This law concerns businesses that store health information.
- PCI DSS (Payment Card Industry Data Security Standards): While PCI DSS isn’t technically a law, failing to protect customer financial data could result in fines and being unable to process credit cards.
- GDPR (General Data Protection Regulation): A strict law that protects the privacy of EU citizens.
- CCPA (California Consumer Privacy Act): A state statute protecting California citizens’ privacy and consumer rights.
Failing to comply with these and other regulations can result in severe legal and reputational penalties.
Maintaining customer trust
Customer trust is a must for any business’s success, and prioritizing data security signals that their information is handled carefully.
But data breaches can erode this trust, tarnishing a brand’s reputation. The effects can be severe and drive an exodus of customers toward competitors.
A 2022 Deloitte study indicates that while customer trust in tech companies is limited, 63% of B2B purchasers highly trust brands that offer a strong security foundation to prevent data breaches.
Mitigating cybersecurity risks
Proactive data security measures act as a potent defense against potential breaches and other cybersecurity threats.
Put simply, the security efforts that stop data breaches from happening will also harden defenses against other dangers, like malware and ransomware.
By staying ahead of potential risks, organizations can ensure the resilience of their digital infrastructure.
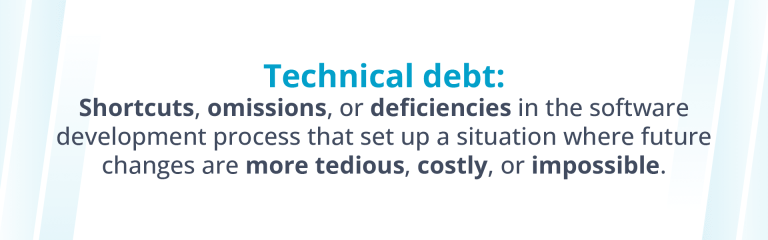
Data security challenges
With so many bad actors vying for access to sensitive and confidential data, securing it is challenging. Here are the top data security risks businesses face:
- Cybersecurity Threats: Malware and ransomware can infiltrate your system, extracting, corrupting, and deleting important files.
- Phishing and Social Engineering: Deceptive techniques can trick employees into handing over sensitive information to those pretending to be legitimate organizations.
- Insider Threats: Whether malicious (employees intentionally leaking information) or negligent (accidental disclosure of sensitive information), actions by employees and contractors can result in breaches.
- Data Breaches: The unauthorized access, disclosure, or acquisition of sensitive data often leads to reputational damage, financial losses, and legal consequences.
- Cloud Security Concerns: Choosing a secure cloud provider to act as your foundation for data security is essential. This is especially vital for enterprises that run on complex systems, like a hybrid cloud, as there are more entry points to safeguard.
Key components of enterprise data security
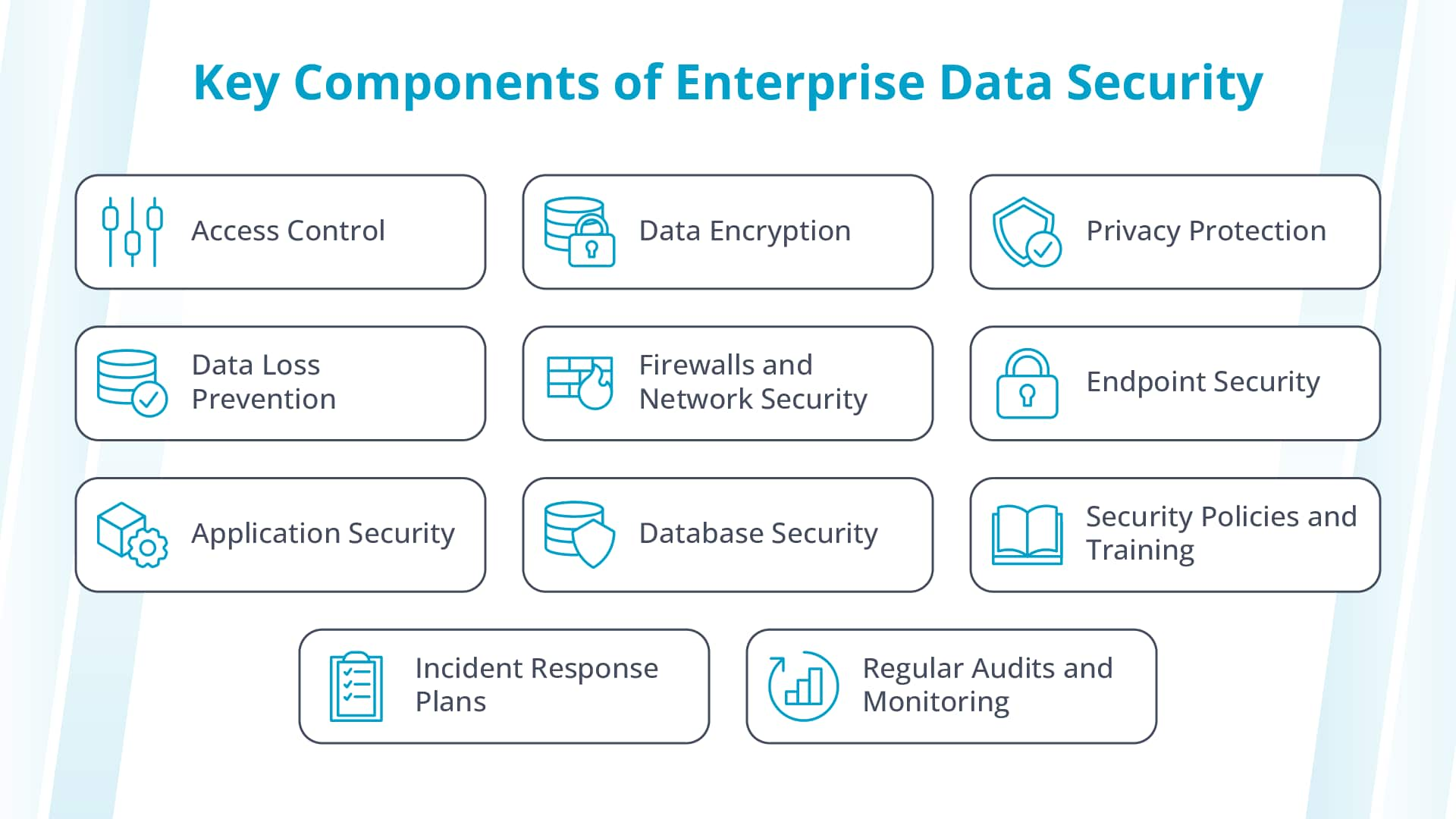
Creating an impenetrable shield for your sensitive data involves a multifaceted approach that faces all of these threats head-on.
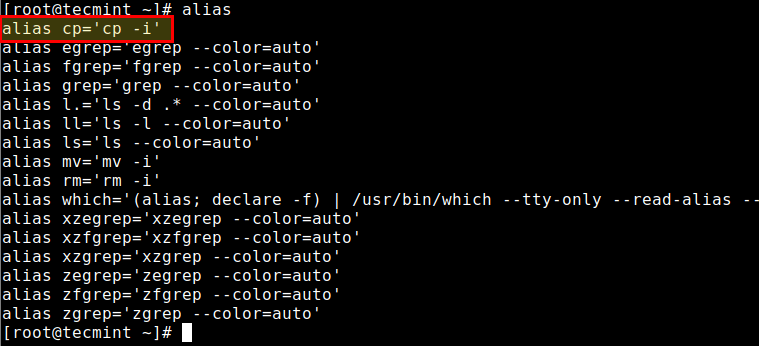
Access control
Access controls ensure that only those who need access to certain data can reach it — the fewer endpoints, the better — limiting potential vulnerabilities. User roles and permissions are an essential part of your data security strategy.
This ensures that only those you trust not to leak classified information will have access to it, and anyone who manages to break into lower-level accounts won’t get anywhere.
Data encryption
Encryption is the process of converting data to secure, unreadable code that can’t be easily decrypted without access keys.
It’s imperative to keep data encrypted when it’s in transit (being transmitted over networks) and at rest (stored on your servers).
Even if hackers get their hands on encrypted data, they’ll have to spend a long time decrypting it before it can be of any use — if they can break through. This at least gives you time to ramp up your security and make a plan.
Privacy protection
Another essential practice is minimizing the amount of personal information collected to limit the impact of a data breach.
You should conduct a Data Protection Impact Assessment (DPIA) when running a project that involves a high risk to individuals’ personal information. This involves analyzing your data collection, use, storage, and deletion policies, as well as how much (if any) personal information is required for the project to succeed.
Data loss prevention

Data Loss Prevention (DLP) is the proactive employment of various policies and tools to monitor, detect, and prevent unauthorized data transfers or leaks.
This involves technologies that identify and block sensitive data from leaving the organization’s network — or can at least trace the source of a leak.
The standards of DLP are very similar to those of general data security, such as implementing access controls and encrypting sensitive data.
Firewalls and network security
Installing a firewall is one of the simplest yet most effective ways to protect your organization’s network infrastructure from external threats. Firewalls scan and filter malicious traffic, preventing it from ever reaching sensitive data.
Endpoint security
One common way attackers sneak in is by exploiting less secure endpoints, such as work phones or on-site computers.
Endpoint security involves securing individual devices (like computers, smartphones, and tablets) to prevent unauthorized access.
Application security
Every application running on a server gives attackers a potential way into the system.
You must protect enterprise data in applications at the root by using secure coding practices to prevent vulnerabilities like cross-site scripting or SQL injections. These practices include input validation and session management.
You should also implement dynamic application security testing (DAST), which simulates cyberattacks to identify vulnerabilities before hackers do.
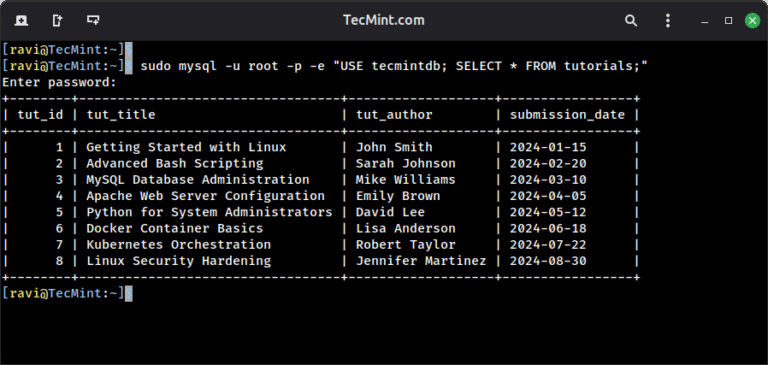
Database security

Applications aren’t the only thing that needs to be protected; the underlying database must also be secured.
To do so, you should encrypt database information, implement automatic database audits, and use strict access controls and authentication.
Security policies and training
Your enterprise should establish and enforce security policies with extensive training to guide employees on handling sensitive information — and how to avoid giving it away.
Incident response plans
This plan will involve identifying, containing, and analyzing security incidents and letting individuals of any level know what to do and whom to contact if they find a data breach in progress.
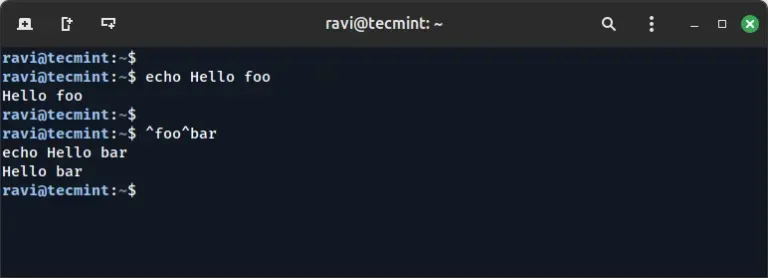
Regular audits and monitoring
Conducting routine security audits is essential to identifying potential vulnerabilities.
Regular monitoring helps you proactively address emerging threats and bolster the overall resilience of the security framework.
Enterprise data security services
When storing swaths of sensitive data, cloud providers play a pivotal role. The security of their underlying systems will assist in keeping your data safe and secure.
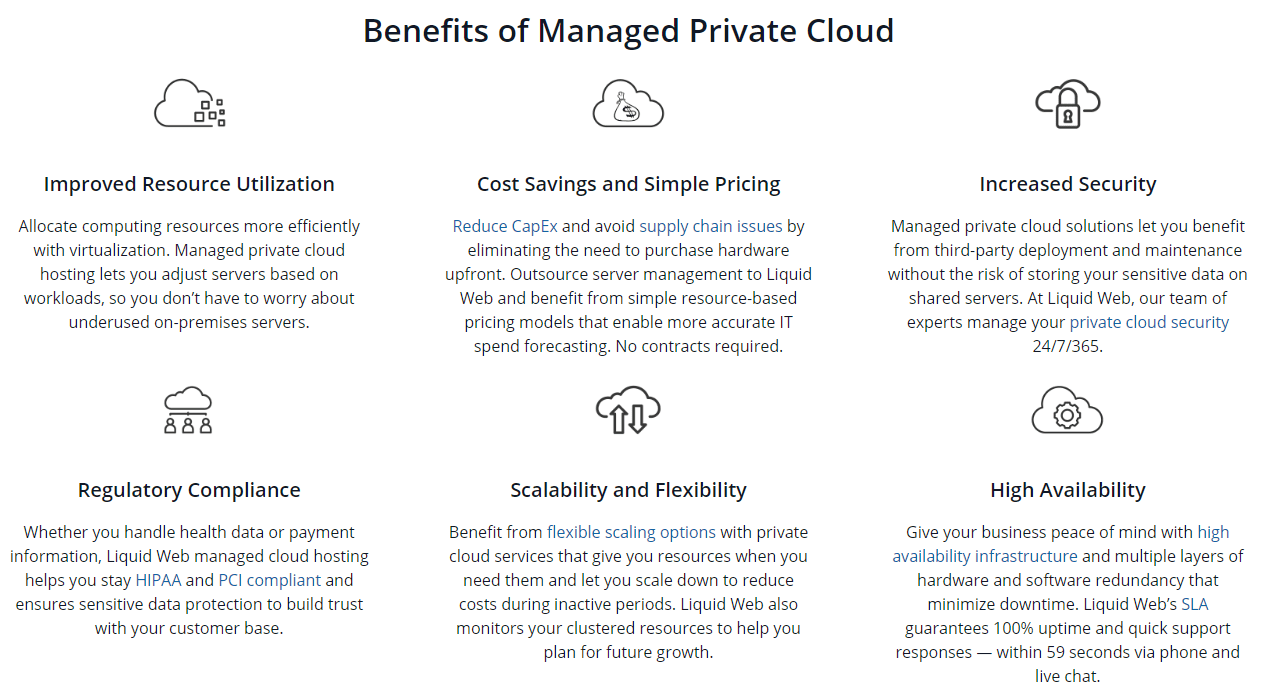
Liquid Web’s private cloud solution provides a secure foundation to bolster your data security. Its features include:
- Managed Hosting: You don’t need to worry about securing the infrastructure. With our self-owned data centers, we handle the hardware, virtual machines (VMs), and cloud platform for you.
- Proactive Security Management: Liquid Web’s security services offer proactive scanning and monitoring for cyber threats, catching them before they infect your servers.
- Security Solutions: Liquid Web’s private cloud service includes a top-of-the-line firewall, distributed denial-of-service (DDoS) protection, and available integrated Acronis backups — all powered on secure servers. You can also purchase advanced DDoS protection.
- High Availability (HA) Infrastructure: Liquid Web’s hardware and software redundancy make data loss a thing of the past.
- Regulatory Compliance: Liquid Web is certified HIPAA and PCI compliant, and we offer specialized HIPAA-compliant hosting with robust physical and network protection. Sensitive financial and health info is safe in our hands. Liquid Web has also earned several other regulation certifications, including for the GDPR.
- Security Add-Ons: If the extensive security options guaranteed with Liquid Web aren’t enough, many security add-ons exist for everything from industry-leading intrusion detection to web application firewalls (WAFs).
Final thoughts: A complete guide to enterprise data security
Protecting your enterprise’s data is a requirement, not an option. Increasing threats inside and outside the business mean your enterprise must harden its defenses and implement foolproof plans to prevent cyberattacks.
While data security starts with your business, Liquid Web provides solid underlying infrastructure to help keep threats out. Our VMware Private Cloud provides the strong foundation your enterprise needs. Our infrastructure is certified, and robust security measures protect our network.