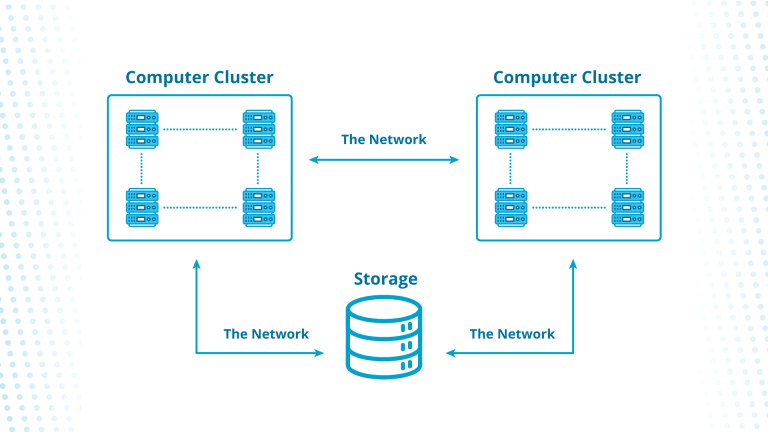
Web server security is a broad term covering the processes and solutions that keep web servers secure. Web server security encompasses three elements: host, network, and physical. For example, a comprehensive firewall can protect network connections, while unauthorized users are prevented from accessing a network by specific hardware or software components.
When discussing web server security, we can look at two key areas:
- Securing a web server’s data
- Securing the services that run on a web server
Access controls and operating system security protect a web server’s data, while antivirus software and firewalls safeguard the services that run on said server. The server’s data can be considered the most important of its assets, which is why it’s likely to be targeted in the majority of attacks.
Fortunately, encrypting information stored on the disk allows you to protect data. Intrusion detection tools can identify unauthorized users’ attempts to intrude, too, and help you respond to them in an effective way.
Ultimately, a user’s priority when using the internet is reaching a specific website as soon as possible. But they want to land on, and use, that website safely. That’s why web server security is such a critical topic, especially today, when hackers have access to highly sophisticated software.
The good news is that professionals in the information technology (IT) industry can take various steps to defend web servers from outside attacks. For instance, implementing a firewall is one of the most basic security measures: these run checks on all traffic going into and out of a web server, identifies traffic that may be dangerous or suspicious, then blocks it. But what else can you do?
In this guide, we’ll explore helpful ways to secure your web server, the best open-source tools, and more. But first, let’s start by discussing why web server security is so important.
Understanding Why Web Server Security Matters
One of the most important parts of having a website is ensuring effective security — particularly when operating a web server. When a web server is unprotected, it can easily become the target of an attack, and hackers could steal sensitive data from it in no time.
Web servers are responsible for numerous tasks, including the storage, processing, and delivery of web pages (as well as other forms of online content). Additionally, web servers are essential for hosting and serving a variety of data in diverse formats. For example, video files, executable programs, and audio files.
With that in mind, a web server should be defended against unauthorized users to ensure that all information on it remains safe. That reduces the risk that anyone can access, modify, disclose, or even destroy data on the server.
What are the Most Common Web Server Weaknesses?
Web servers deliver the web content you browse daily, and they’re designed to be as robust, efficient, and secure as possible. However, they still have a number of vulnerabilities that affect their (and their users’) security.
Common weaknesses include command injection, cross-site scripting (XSS), and SQL injection. While some of these are easy to take advantage of, exploiting others requires a little more work and detail. Below, we’ll take a closer look at these security threats and why they’re so dangerous.
DoS Attacks
When someone launches a denial of service (DoS) attack, they are trying to prevent users from accessing the targeted web server or network resource as they usually would.
These focus on a specific web server or resource: the attacker floods the target with high levels of traffic until it becomes unavailable to genuine users. That can be especially damaging for online retail sites, as they would be unable to process transactions.
Perpetrators launch DoS attacks using viruses, bots, or other tools that consume the target’s CPU or network capacity. They can also initiate attacks with computers or networks that have been infected by viruses or other harmful software.
Cross-Site Scripting Attacks
During cross-site scripting (XSS) attacks, perpetrators inject code executed by the user’s web browser. The code responsible is typically seized when the user’s cookies are sent to the web server.
Perpetrators tend to use XSS attacks to undertake actions on behalf of a user, which allows them to access a user’s current session.
SQL Injection Attacks
An SQL injection is a form of attack capable of overrunning a database. The attacker will input malicious code into the information entry fields on a data-driven application or website.
Once the code is injected into the database of a website or application, the attacker can access data that would normally be out of their reach. They can view and tamper with this information, which could allow them to manipulate and expose sensitive data.
How to Keep Your Web Server Secure
In our interconnected world, companies of all sizes must take web server security seriously to stay safe. Cybercriminals have a wide variety of techniques to choose from, so it’s vital that you implement the necessary measures to secure your web server.
Attackers can cause extensive damage to any business, but comprehensive security can make their work much more difficult. Here are three simple steps to keep your web server secure.
Top Open Source Security Solutions for Web Servers
You can choose from a wide range of open source security tools to protect your web server. These can help defend you against common threats and provide users with a safer experience.
Here are the best open source security tools for web servers available.
Nmap
Nmap (Network Mapper) is an open-source solution for security audits, discovering networks and hosts, and exploring networks. You can use Nmap to scan networks on a bigger scale, but it’s suitable for single hosts too.
Snort
Snort is built for preventing network intrusion and identifying potential threats. It can run traffic analysis in real-time, using both protocol analysis and pattern matching to pinpoint signs of possible issues in network traffic.
Metasploit
With Metasploit, you can get an insight into security weaknesses that will make it easier to protect your web server.
Metasploit helps in IDS signature development and penetration testing, so you can learn more about vulnerabilities and take action to address them before they are exploited by attackers.
Sqlmap
Sqlmap is an open-source tool for automated security testing: you can automatically identify and exploit SQL injection vulnerabilities that would allow attackers to take a database over. This can be an effective way to fix weaknesses before someone else discovers them.
OpenVAS
With OpenVAS, you can run a comprehensive network scan to detect issues (such as XSS vulnerabilities). OpenVAS is free to use, and companies across the globe use it to maintain a secure infrastructure.
Summary
Operating a website of any kind requires a good web server. The site’s core files are hosted on a computer and delivered to the users who land on your site, so ensuring effective web server security is paramount to reduce risks. Otherwise, attackers could target your site, access sensitive data, and disrupt your operations.
We hope this guide to web server security has helped you understand some of the risks out there and the best ways to stay safe.